information security assessments
Tailored Information Security Assessments, Comprehensive Results
Whether your organization is just beginning to develop an information security program or if you already have a mature program that you’re looking to enhance, a FireOak information security assessment can help your organization develop, supercharge, or fine-tune your program.
Our team of experts conducts organizational information security assessments that broadly examine people, processes, and technology to reveal a holistic view of an organization’s security posture. For holistic assessments, we use a mix of tabletop exercises, interviews, policy and document review, and a high-level review of your technical architecture.
Alternatively, the FireOak team can take a comprehensive look at how your organization has configured an deployed a specific cloud platform. For these assessments, we conduct an in-depth review of cloud platforms such as Microsoft 365, Google Workspace, WordPress, Salesforce, Monday.com, ClickUp, Asana, and more. We look at configurations, integrations, access controls, backups, internal and external knowledge sharing, and much more.
Regardless of whether the assessment is organizationally-focused or zeros in on a single platform, we use a risk-based analysis and emphasize how vulnerabilities can be leveraged by attackers to gain access to an organization’s confidential information, data, and systems.
Information Security Assessments:
The FireOak Difference
A few highlights about what sets apart all of our assessments:
1
Actionable
Our reports are chock-full of practical, actionable next steps. Your team will know what to do.
2
Prioritized
At the end of the report, we’ll include a high-level overview of next steps, in priority order.
3
Comprehensive
In addition to the written report, we’ll include the output from our technical evaluations.
4
Business Oriented
The report will include an executive summary designed for organizational leaders.
5
Q&A with Execs
We’re available to talk with senior executives, board members, or your full leadership team.
6
Knowledge Transfer
As part of our wrap-up, we’ll debrief with your tech team and will answer their questions.
People, Processes, and Technology
For Business Leaders & IT
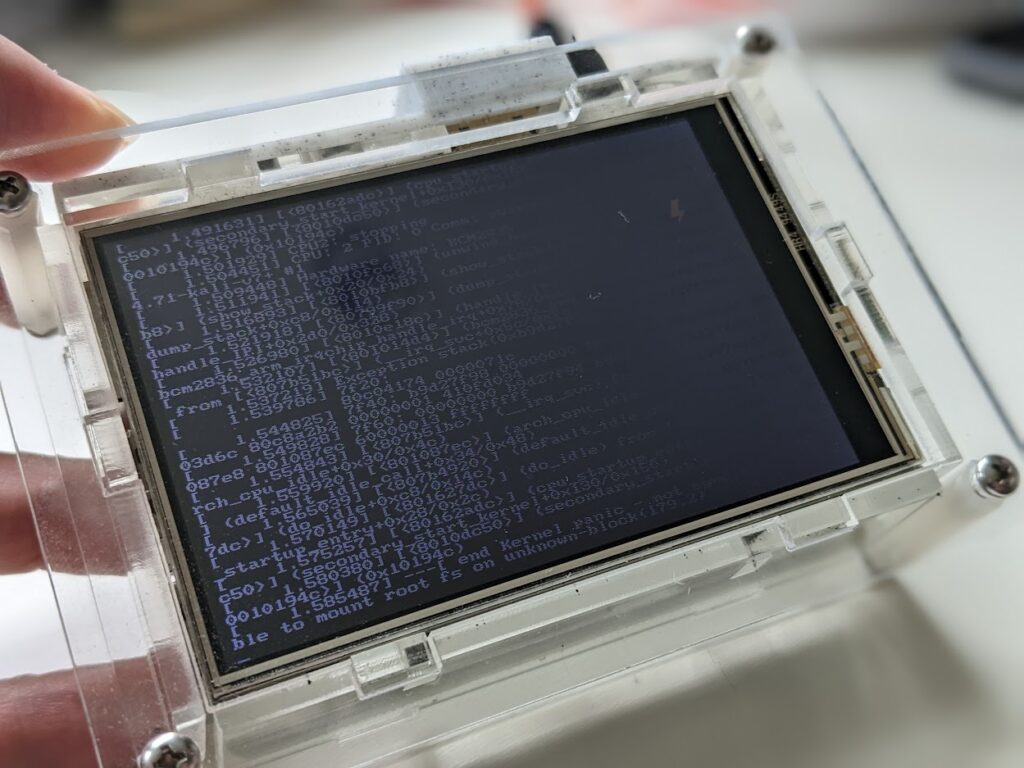
From a technical perspective, these assessments include details on all of the vulnerabilities present in a network, along with clear examples of how these vulnerabilities can be exploited in the current environment. Business leaders appreciate the clear explanations of how systems can be exploited and what the risks are to their organization. IT leaders appreciate the comprehensive technical details included in findings.
Ready to get started?